Το Uid.me είναι ένα εργαλείο δημιουργίας ιστοσελίδων που δημιουργήθηκε από τη ρωσική τεχνολογική εταιρεία uCoz. Με κεντρικά γραφεία στη Μόσχα,...
Διάβασε εδώΔισεκατομμύρια χρήστες Android σε όλο τον κόσμο ενδέχεται να επηρεαστούν από μια νέα ευπάθεια στο WiFi, την οποία οι χάκερ...
Διάβασε εδώΠερισσότερα από 1,3 εκατομμύρια αρχεία της Insomniac Games, η οποία ανήκει στη Sony (6758.T), συμπεριλαμβανομένων σχεδίων παιχνιδιών, προϋπολογισμών και πληροφοριών...
Διάβασε εδώΤο μεγαλύτερο κινητό πάροχο υπηρεσιών τηλεφωνίας της Ουκρανίας, η Kyivstar, ανακοίνωσε την Τετάρτη ότι έχει αποκαταστήσει όλες τις υπηρεσίες της...
Διάβασε εδώ Hacking Tutorials
Hacking Tutorials Σήμερα, το Bluetooth είναι ενσωματωμένο σε σχεδόν όλες τις συσκευές και gadgets μας. Στους υπολογιστές μας, τα smartphones, τα iPods,...
 Hacking Tutorials
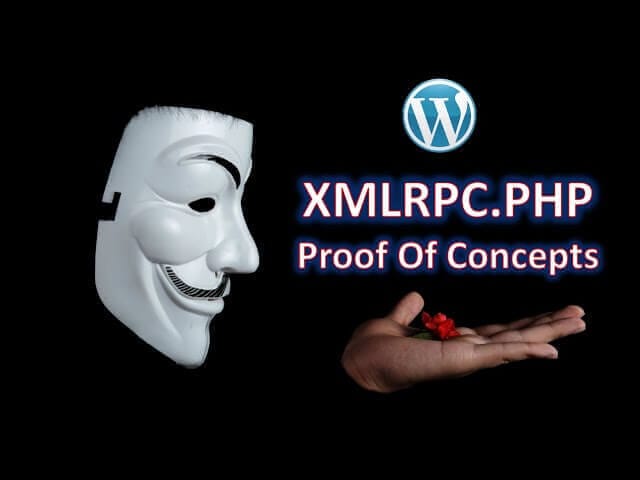
Hacking Tutorials Το XML-RPC (XML Remote Procedure Call) είναι ένα πρωτόκολλο επικοινωνίας που επιτρέπει σε εφαρμογές να επικοινωνούν μεταξύ τους μέσω του...
 Hacking Tutorials
Hacking Tutorials Συχνά, θα έχετε τη δυνατότητα να ανεβάσετε ένα αρχείο σε ιστότοπο, όπως ένα αρχείο Word, ένα PDF ή μια εικόνα...
 Hacking Tutorials
Hacking Tutorials Τα exploits αντιπροσωπεύουν μια σημαντική πτυχή του κυβερνοχώρου, καθώς αναδεικνύουν τις ευπάθειες στο λογισμικό, τα λειτουργικά συστήματα και τις εφαρμογές....
 Hacking Tutorials
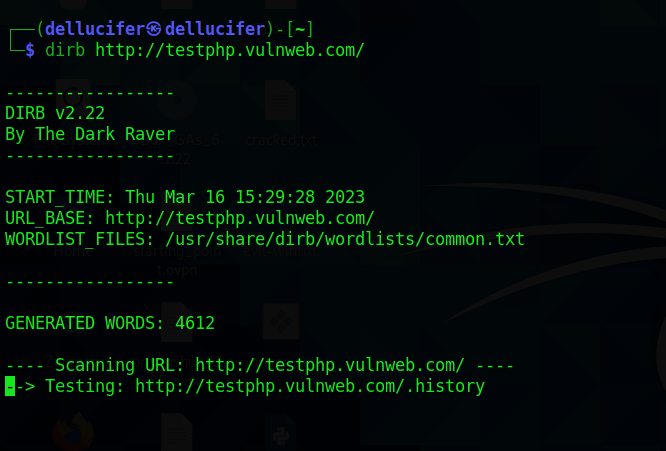
Hacking Tutorials Το Dirb είναι ένα εργαλείο ανοικτού κώδικα για την εξερεύνηση καταλόγων σε ιστότοπους. Πρόκειται για ένα εργαλείο σάρωσης καταλόγων (directory...
 Hacking Tutorials
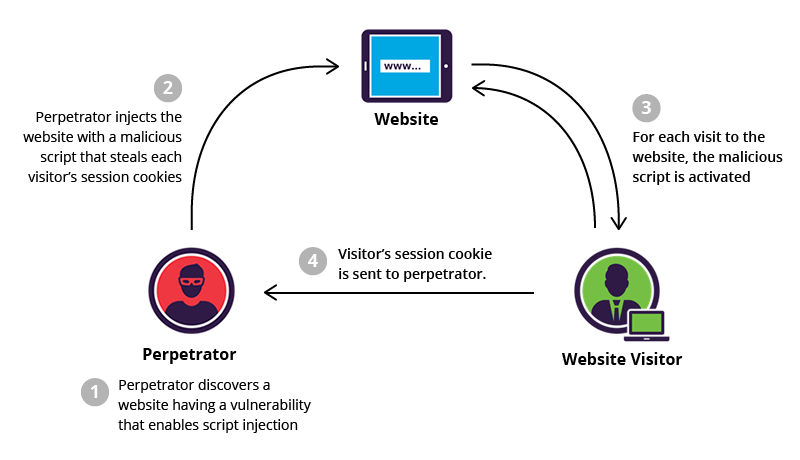
Hacking Tutorials Το XSS (Cross-Site Scripting) είναι μια επίθεση κατά της ασφάλειας των ιστοσελίδων, κατά την οποία ο επιτιθέμενος ενσωματώνει κακόβουλο κώδικα...
Ήρθε η ώρα να προσπαθήσουμε να εκτελέσουμε buffer overflow (με ανακατεύθυνση) σε ένα λειτουργικό σύστημα Windows 11. Για να δούμε...
ShellCodes In hacking, a shellcode is a small piece of code used as the payload in the exploitation of a...
0x0. Εισαγωγή A buffer overflow (bof), or buffer overrun, is an anomaly whereby a program, while writing data to a...
Το συγκεκριμένο άρθρο είναι το πρώτο μέρος μιας σειράς που θα περιγράψει την αδυναμία Buffer Overflow. Σε αυτό το πρώτο...
Το spoofing είναι μια κακόβουλη εφαρμογή που συγκαλύπτει μια νόμιμη πηγή για να αποκτήσει ευαίσθητες πληροφορίες ή για να αποκτήσει...
Το Macchanger στο Kali Linux αποτελεί ένα ισχυρό εργαλείο που επιτρέπει στους χρήστες να αλλάξουν τη διεύθυνση MAC της δικτυακής...
Στη σημερινή ζωή, είμαστε περιτριγυρισμένοι από πολλά εργαλεία ασφάλειας και ανωνυμίας τα οποία υπόσχονται να μας παρέχουν κάποια προστασία. Αλλά...
ΣΗΜΕΙΩΣΗ Αν σας ενδιαφέρει η προστασία της ιδιωτικής ζωής στο Internet τότε πρέπει να πάρετε αυτόν τον οδηγό πολύ σοβαρά. Το παραμικρό λάθος,...
VPN ή Proxy: Ποια είναι η Καλύτερη Επιλογή; Καθώς η ψηφιακή ασφάλεια και η ιδιωτικότητα στο Διαδίκτυο γίνονται όλο και...
Υπάρχουν πολλές μηχανές αναζήτησης που έχουν ως κύριο χαρακτηριστικό την προστασία της ανωνυμίας των χρηστών και τον σεβασμό της ιδιωτικής...